The global trade in counterfeit goods, estimated at $500 billion annually, severely damages brand value and consumer trust. For luxury watches, high-end apparel, premium spirits, and pharmaceuticals, the challenge is twofold: securing the supply chain and empowering the end-user. Near Field Communication (NFC) technology, with its unique advantages, effectively addresses this challenge by turning every smartphone into an interactive product verification tool.
From Sealed Supply Chain to the Consumer’s Hands
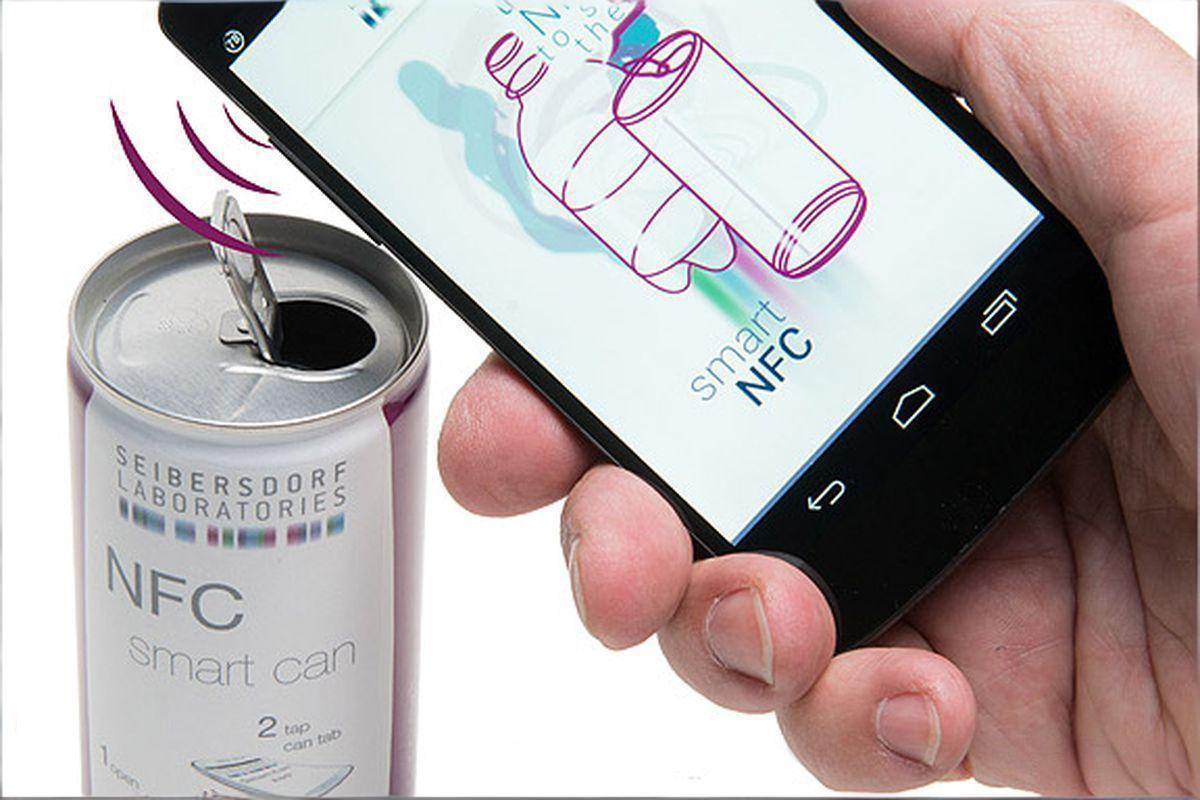
While RFID systems offer robust back-end tracking capabilities, NFC technology brings the verification process directly to the consumer. A simple tap of a smartphone on an NFC-enabled product tag initiates a secure dialogue. This process verifies product authenticity, displays detailed product provenance information (item-level tracking), and can even unlock exclusive digital content, creating a powerful brand engagement experience.
Key Advantages of an NFC-First Anti-Counterfeiting Strategy:
- Providing Consumers with Irrefutable Proof: Technologies like NFC tamper-evident tags are designed to be destroyed upon removal. If the tag is intact and verifies successfully, the product is authentic. This physical layer of security makes large-scale replication virtually impossible for counterfeiters.
- Building Trust and Enhancing Engagement: Successful verification can lead consumers to a verified portal with product origin stories, usage instructions, or owner registration. This transforms a security check into a brand experience, fostering customer loyalty.
- Actionable Data Insights: Every tap generates data. Brands can map verification attempts in real-time, identify the geographical distribution of fraudulent attempts, and gain insights into consumer engagement patterns.
Q&A
1.Is implementing NFC tags expensive?
The return on investment is significant. Compared to the revenue losses caused by counterfeiting and the long-term value of enhanced customer trust and loyalty, the cost of embedding NFC tags is negligible. It’s an investment in brand value.
2.Can NFC tags be copied?
Modern solutions utilize secure and uniquely encrypted chips. Combining this with cloud-based authentication platforms and tamper-evident designs (such as fragile labels) allows for the construction of a multi-layered defense system, making it difficult to compromise at a low cost. Product Focus: Customized Solutions for High-Value Scenarios
For brands looking to implement this strategy, choosing the right label is crucial. RFIDHY’s NFC solutions offer a range of products to meet diverse needs:
- HY-NTL Fragile NFC Labels: Ideal for luxury packaging. Their tamper-evident design ensures single-use, providing visual and digital proof of tampering – perfect for luxury product anti-counterfeiting.
- HY-M00707 HF Micro Tags: Featuring a tiny, robust epoxy resin encapsulation, these can be directly embedded into small, high-value items such as high-end accessories, enabling secure product authentication.
- HY-UJT UHF Jewelry Tags: Offering a longer reading distance, these facilitate inventory management in retail store backrooms while still supporting consumer-facing interactions, connecting supply chain visibility and end-user engagement.
By deploying smart NFC tags, brands can not only combat counterfeit products; they can also build transparent, efficient, and trustworthy relationships with customers, transforming product protection into an interactive experience.